In a perfect world, email can only be read by the user the email was intended for. In the real world however, things are a bit different.
Although email can easily be encrypted, most email is not. Roughly speaking there are two ways email can be leaked: it can be read in transit (i.e., when sent over the Internet), or it can be read at rest (i.e., after the email is stored). Email is only briefly in transit. Once an email has reached its destination, it is no longer in transit. An email is however stored until it is deleted (and even then there will probably be a backup somewhere). It is therefore more likely that an email gets leaked after storage and not during transmission (for example, if your account gets hacked, the hacker can read all your email).
So even if your email is transmitted in plain text, encrypting the email before storing it will be very helpful to protect yourself against some hacker trying to break into your mailbox (or to protect yourself against Gmail for scanning your email for targeted ads).
We will show how you can store all incoming email in encrypted form on an external mail server with the CipherMail email encryption gateway, even if an incoming email is not encrypted.
Using the Mailvelope browser extension, you will still be able read your email online. The browser extension will locally decrypt the email when the email is opened. We use a similar setup ourselves to create a remote encrypted backup of all our incoming email on Gmail. Since every email is encrypted, Gmail cannot read the content of the emails.
For the rest of this post we assume that all email will be stored on a Gmail server. However, the same principle can be used with other mail providers just as long as the mail provider is supported by Mailvelope (Mailvelope supports Gmail, Outlook.com, Yahoo and other Webmail providers).
Prerequisite
Since all incoming email must be encrypted before being sent to Gmail, all email must first be sent to the CipherMail email encryption gateway. This requires that you need to use your own domain name (which is a good thing to do anyway). Also a functional instance of the CipherMail gateway is required.
Setup
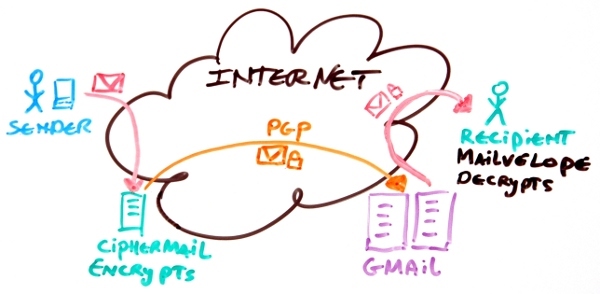
When an email is sent by some external sender, it is first sent to your CipherMail gateway (since the mx records of your domain point to the IP of the CipherMail gateway). The CipherMail gateway then PGP encrypts the message and forwards the message to your Gmail account. When the email is opened by the recipient, the Mailvelope extension will decrypt the message automatically. The following diagram gives an overview of the mail flow:
The following part will briefly explain the required steps on how to setup the above configuration.
- Install a CipherMail gateway.
- Forward all email to Gmail.
- Install Mailvelope.
- Create a PGP secret key in Mailvelope (or import and existing key).
- Import the PGP public key into the gateway.
- Configure the gateway.
Install a CipherMail gateway
A running instance of the CipherMail gateway is required. You can download a Virtual Appliance for VMware or HyperV. Alternatively the gateway can be installed using the installation packages for Ubuntu, Debian, Red Hat/CentOS or OpenSUSE.
Forward all email to Gmail
After the email is encrypted by the gateway, the email must be forwarded to the Gmail server. The forwarding configuration depends on whether Google apps for business is used. With Google apps for business you can configure Gmail to accept email for your own domain. If Google apps for business is used, the "Internal relay host" setting should be set to the Gmail domain to forward all incoming email to Gmail. If a personal Gmail account is used, forwarding to Gmail can be configured by setting a virtual alias in Postfix (repeat this step for all recipients that must be forwarded).
Install Mailvelope
Mailvelope is a browser extension which supports OpenPGP. Mailvelope can locally decrypt and encrypt email using secret key stored locally in the browser. Mailvelope currently only supports Chrome. A Firefox version is currently under review by Mozilla for inclusion in the Mozilla add-ons store.
Create a PGP secret key in Mailvelope (or import and existing key)
Mailvelope requires an OpenPGP for decrypting the email. A new secret key can be generated by Mailvelope or an existing secret key can be imported from a secret keyring. See Mailvelope help for instructions on how to generate or import a key. For every recipient a PGP secret key should be created.
Import the PGP public key into the gateway
The gateway needs the PGP public key of the secret key(s). For every secret key generated or imported in the previous step, the public key should be imported into the gateway. This can be done by either importing the key from a file or, if the key is published on a key server, the key can be imported from the key server. The key should be trusted by the gateway otherwise the key will not be used.
Configure the gateway
The gateway should be configured to always encrypt for the forwarded recipient(s). To always encrypt for a recipient, set the "Encrypt mode" for the recipient to "Allow (sender or recipient)". The CipherMail gateway by default encrypts with PGP/MIME. Mailvelope however only supports PGP/INLINE. The recipient(s) should therefore be configured for PGP/INLINE.
Reading encrypted email
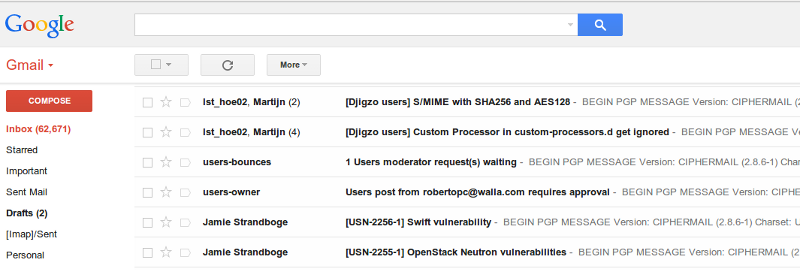
All email forwarded to Gmail will now be encrypted as can be seen from the inbox.
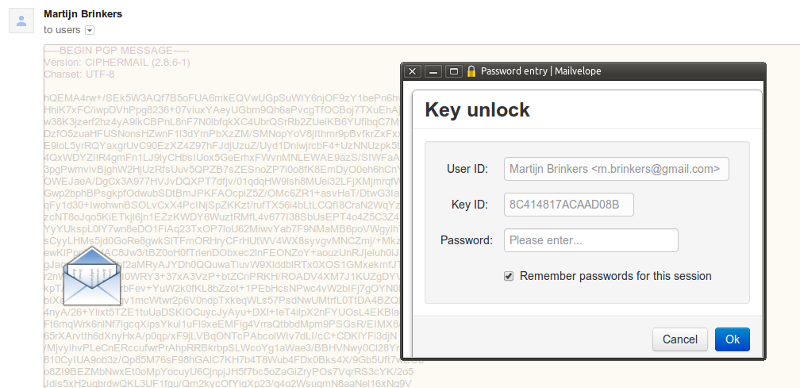
When an email is opened, Mailvelope is activated. The user needs to enter the secret key password to read the encrypted email.
Discussion
With this setup, all incoming email will be encrypted and then forwarded to Gmail. Encrypting all email however has a couple of shortcomings which we will discuss.
Searching
Since all email will be encrypted, searching for an email based on content will no longer work. You can only search based on meta data (like sender, subject, date etc.) since the meta data is not encrypted.
Attachments
Attachments cannot be decrypted. This is a shortcoming of the Mailvelope extension. Attachments should therefore be downloaded and decrypted locally with GnuPG. If you are using a mail client with PGP support, for example Thunderbird with Enigmail, attachments are directly supported.
HTML email
Since Mailvelope currently only supports PGP/INLINE, HTML email is not supported (HTML email is supported with PGP/MIME). The CipherMail gateway will convert HTML only emails to text before encrypting with PGP/INLINE. We are investigating whether we can support HTML with PGP/INLINE.
Sending email
With the current setup, only incoming email will be encrypted. Email sent from Gmail with your browser will by default not be encrypted. To support encryption of all sent email, even if the recipient does not use PGP, requires some changes to Mailvelope. Mailvelope should be configured to always encrypt with one particular PGP key. Gmail should then be configured to relay via the external CipherMail server. The CipherMail server will decrypt the message and then relay the message to the intended recipient. This ensures that even sent items are encrypted.